In a hurry and just want the script, click here.
If you're here, then you must have a driver and App-V conundrum. Perhaps you have sequenced scanner software but you still need to find a delivery method to get the driver injected? Maybe it’s a label maker, a noise measurement tool, a 3d printer, timing equipment - the list goes on.
You’re in the right place. I've written a script which will work with App-V to inject and remove the drivers as part of the DeploymentConfig. It will also handle drivers where the certificate is not known in the Trusted Root Certification Authorities.
The script was written with the following in mind.
· Scalable.
· Reusable.
· Low administrative overhead.
A Quick Guide On Drivers
First, some knowledge on drivers, driver signing and how it all works together. After much research I've found drivers fall into three categories.
·
Signed and certificate
chain is recognised in the Trusted Root Certification Authorities.
These will silently install with DPIsnt.
·
Signed, but certificate
chain is not recognised by Trusted Root Certification Authorities.
These will throw a prompt when you try to install them with DPIsnt.
·
Unsigned or signed
but has been modified, the certificate may or may not be recognised by the
Trusted Root Certification Authorities.
These will throw an ugly warning which you cannot get around easily.
You can work around the second bullet point, but to work around the third bullet point is either impossible or a lot of work depending on your desired outcome. If this is your problem, then read "Sign your unsigned drivers - Damn It" for more information, as this script will not help.
At this point I recommend reading the sections below from "Practical Windows Code and Driver Signing" - it will give you a decent insight into driver signing.
· Anatomy of a signature
· Signature requirements, specifically the section TRCA requirements for it to look good.
· Installing a driver package
· Driver package installation in Windows Vista and 7
Important information: The .cat file contains a cryptographic hash of all the files, if you modify any of the files it will break the hash. eg, editing of the .inf file.
All About The Manage-Drivers.ps1 Script
The script can be found here on my GitHub Gist.
https://gist.github.com/rileyz/464175e3bb96f1b67dfc
The script can perform the following functions.
- Inject drivers.
- Inject drivers and hide Programs and Features entry.
- Import certificate into Trust Publishers store pre driver injection.
- Remove drivers.
- Remove certificate from Trust Publishers store post driver removal.
- All the above with Logging.
There are a number inbuilt script variables that can be changed as per requirements, they are as follows.
$LogFile, change this to your desired log location. Default is %Windows%\Temp
$DPInst32, name of DPInst 32bit executable.
$DPInst64, name of DPIsnt 64bit executable.
$WithThisErrorCode, set to 0 to gracefully exit or set to 1 to fatally exit.
It’s important to note that if you plan to use $WithThisErrorCode to fatally exit, it needs to be used in conjunction with the DeploymentConfig xml attribute <Wait RollbackOnError="true" Timeout="30"/>.
The script has two mandatory parameters which are as follows.
-DriverSource a token, UNC or relative path to driver source.
-LogName the name for the log file.
The script has two optional parameters which are as follows.
-HideARP, this switch will not add entry to Programs and Features.
-Remove, this switch will remove the driver package from the Driver Store.
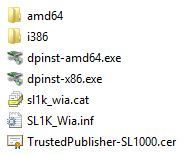
If your certificate chain is not recognised by Trusted Root Certification Authorities then you need to add a certificate to the Trusted Publishers certificate store. This functionality has been built into the script, just prefix the certificate with “TrustedPublishers” and store it at the base directory with the drivers.
To make use of the script, the DeploymentConfig will need to be edited. The script is launched via PowerShell in ExecutionPolicy ByPass mode, passing the required arguments to the script to locate the drivers and name the log file.
To inject drivers, where the drivers are located on the VFS.
<AddPackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "..\Root\VFS\ProgramFilesX86\DriverFolder" -LogName "Example.log"</Arguments>
To inject drivers, where the drivers are located in a zip archive.
<AddPackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "DriverArchive.zip" -LogName "Example.log"</Arguments>
To inject drivers and hide the Program and Features entry.
<AddPackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "DriverArchive.zip" -LogName "Example.log" -HideARP</Arguments>
To remove a driver, where the drivers are located on the VFS.
<RemovePackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "..\Root\VFS\ProgramFilesX86\DriverFolder" -LogName "Example.log" -Remove</Arguments>
To remove drivers, where the drivers are located in a zip archive.
<RemovePackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "DriverArchive.zip" -LogName "Example.log" -Remove</Arguments>
Step By Step Guide
Best to do the steps below in a virtual environment as it’s easy to step back to a clean snapshot for testing.
Remember, always do a standard vendor install to ensure the software/drivers work as required.
I'm assuming intelligence on the reader’s part to fill in the gaps.
- On a clean
machine inject the drivers manually using DPInst.

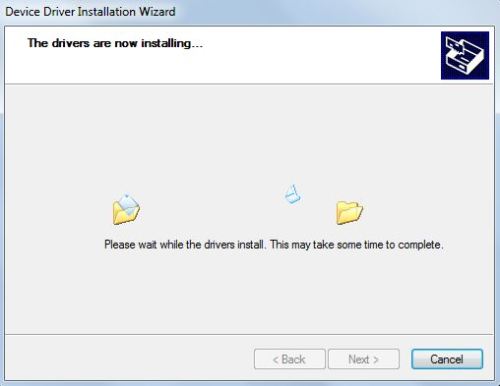
If you get prompted “Would you like to install this device software?” then check the “Always trust software from…” check-box and click install.
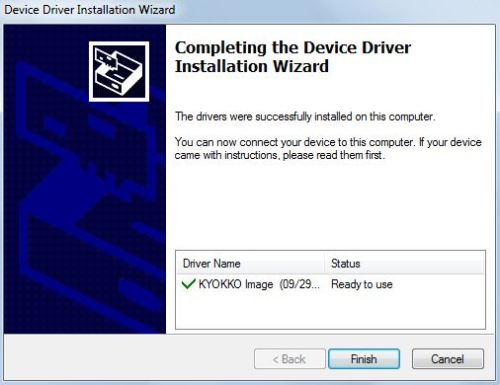
Open the DPIsnt log to double check it installed ok. Returning with code 0x100 means DPInst injected one driver, 0x200 means two drivers injected and so on.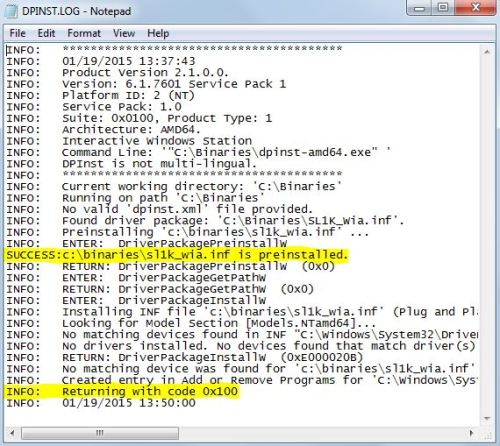
- If you
received the “Would you like to install this device software?” prompt, it
means the certificate chain was not recognised in the Trusted Root
Certification Authorities. Hopefully you checked the box “Always trust
software from…” as we now need to export the certificate from the
certificate store.
In a nutshell you need to start MMC -> Certificates -> This Computer -> Trusted Publishers -> export the certificate.
If you’re a bit unsure then have a look at the two links below for more detailed information, no point reinventing the wheel.
http://it.peikkoluola.net/2013/12/16/windows-cant-verity-the-publisher-of-this-driver-software-bat
http://www.myangrydome.com/?p=1744 - After the above
steps one and two you should have similar files below ready for the App-V
package, to either add during sequencing or afterwards during finalisation
of the App-V package.
- Time to
sequence your application and add the files to the VFS or scripts
collateral folder depending on your desired implementation.
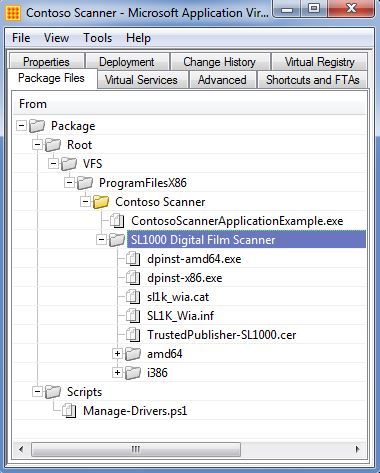
You should have something similar below after you have sequenced the application.- VFS
implementation.
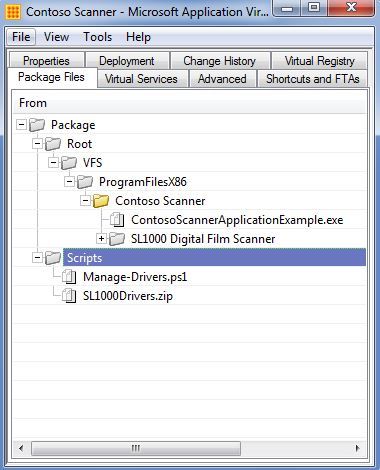
- Scripts
collateral implementation.
- VFS
implementation.
- It’s now time
to edit the DeploymentConfig.xml, the implementation you chose in step four
will determine the PowerShell arguments you need to pass to the script.
<AddPackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "[{ProgramFilesX86}]\Contoso Scanner\SL1000 Digital Film Scanner" -LogName "ContosoScanner.log"</Arguments>
<Wait RollbackOnError="true" Timeout="30"/>
</AddPackage>
<RemovePackage>
<Path>powershell.exe</Path>
<Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "[{ProgramFilesX86}]\Contoso Scanner\SL1000 Digital Film Scanner" -LogName "ContosoScanner.log" -Remove</Arguments>
<Wait RollbackOnError="false" Timeout="60"/>
</RemovePackage>
<AddPackage> <Path>powershell.exe</Path> <Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "SL1000Drivers.zip" -LogName "ContosoScanner.log"</Arguments> <Wait RollbackOnError="true" Timeout="30"/> </AddPackage> <RemovePackage> <Path>powershell.exe</Path> <Arguments>-ExecutionPolicy ByPass -File Manage-Drivers.ps1 -DriverSource "SL1000Drivers.zip" -LogName "ContosoScanner.log" -Remove</Arguments> <Wait RollbackOnError="false" Timeout="60"/> </RemovePackage>
- Where do I get DPInst?
You can get DPInst from the Windows Driver Kit (WDK).
Compatible With App-V Versions
If the version has not been mentioned, then it has not been tested against that version.
Most likely will be OK, just has not been formally tested.
- App-V 5 SP2 - OK
- App-V 5 SP2 HF4 - OK
- App-V 5 SP3 - OK
- App-V 5.1 - OK
- App-V Windows 10 (all versions with no known issues currently 27/11/2019)
Compatible With Windows Installer
Just tested this out recently on a Windows Installer package, I had a requirement to add the certificate to Trusted Publishers as that was stopping the driver injection. It works but it not intended for this kind of application.
Edit Log
29/01/2015: Initial release.
24/02/2015: Spelling errors fixed.
10/04/2015: Added App-V target version testing.
17/06/2015: Confirmed script works on SP3.
13/11/2015: Confirmed script works on MSI packages.
*Seen issues with zip extraction on Windows 7, recommend folder path for source.
19/04/2016: Confirmed script works on 5.1.
Caveats, bug found when running script with ScriptRunner.exe.
Test case = Windows 10 64-bit, App-V 5.1.
Script detects 64-bit system as 32-bit, thus uses incorrect DPInst architecture.
The root cause is ScriptRunning.exe being 32-bit, thus running a 32-bit PowerShell session.
16/05/2016: Script has been bugfixed to detect o/s architecture correctly when launched with ScriptRunning.exe.
03/05/2017: Bug found: Script does not unpack zip file from UNC path reference location, ie \\MyServer\MyDriver.zip.
This is an unusual/low risk bug as normally the zip source is stored with the package itself.
27/11/2019: Updated App-V Support.

Comments