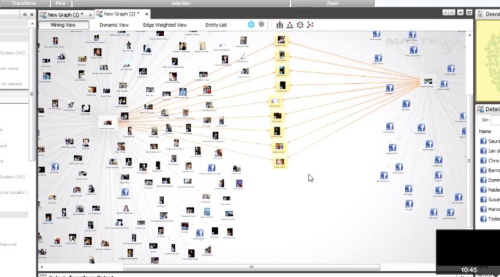
Nicholas Arvanitis, Security Consulting Services, Dimension Data (@narvanitis) provided some interesting stories and examples about how personal public information can be used to gain access to sensitive business information. The premise was why attack a company which is so well protected when attackers can instead go after employees who are sharing lots of personal information online. Some examples of different social media outlets and the kinds of information one can gain and how it may be used were provided. There are tools now that can analze publicly available employee information between companies to gain insight into who is working with who to make assumptions about such relationships. One can even gain enough information to follow through and try to confirm such assumptions.
It was a very enlightening session, but no silver bullets were offered in terms of how to deal with the problems. Today, it would seem awareness and general employee education of safe use are the only realistic solutions.
There are no tools to watch what people are posting today. Some organizations might be compelled to just block it all, but this often not a realistic solution—it is important to understand how different groups use social media. Policies and training geared at making users aware of risks and conveying some examples of how it can be damaging are the most powerful tools to social media security right now. Technological solutions are starting to move toward context-aware security controls, which will serve, to block applications (even specific capabilities within an application such as chat within Facebook) and not ports. Such controls can further apply to the role of a user to be a very effective solution.
In short, when it comes to social media security, be prescriptive to users and ensure they are aware of what is acceptable.

Comments